Threat 1: AI-Powered Phishing
Surgically Precise Emails Your Team Cannot Ppot
AI analyzes court filings, firm websites, LinkedIn profiles, and prior email patterns to craft messages that are contextually perfect. No typos. No generic greetings. Your real case name, your real colleague, your firm’s exact tone.
Standard spam filters were built to catch the old generation of phishing — suspicious domains, generic keywords, structural red flags. AI-generated phishing contains none of these. It bypasses technical filters and human instincts simultaneously.
The attack chain is fast. Credentials captured, network mapped, ransomware positioned — all within hours. The average time from a single click to full network compromise is four hours.
Law firms are especially exposed. Legal culture runs on urgency and trust: when an email references a real deadline and comes from a familiar name, the instinct is to act, not verify. Attackers engineer exactly this pressure.
4 hours
Average time from phishing click to full network compromise
Source: IBM Threat Intelligence 2025
The defense requires AI fighting AI: behavioral email security that detects anomalies rather than keywords, link sandboxing that evaluates URLs before anyone clicks, and MFA everywhere so that stolen credentials alone are not enough to compromise your systems. Monthly phishing simulations, not annual checkbox training are the difference between a team that recognizes these attacks and one that doesn’t.
Threat 2: Voice Cloning
Three Seconds of Audio is All It Takes
AI clones a voice from any public recording — a podcast, a video, a recorded CLE — and produces a perfect replica. The attacker calls your bookkeeper, paralegal, or associate, sounds exactly like your managing partner, and requests an urgent wire transfer.
“Hi Sarah, it’s David. I’m in a client meeting, wire $75,000 to the settlement account before 4 PM. I’ll send the details now.”
The voice is identical. The scenario is plausible. The instructions arrive by email from a spoofed account. And $75,000 is gone.
Voice cloning attacks work because law firms run on trust. Partners are often unreachable. Deals are always urgent. That professional culture, weaponized by AI, becomes a liability.
One rule stops 100% of voice cloning attacks: any wire transfer request, regardless of who it appears to come from, requires verbal confirmation on a pre-established number from your contacts or firm directory. Not the number that called you. A number you already have. Thirty seconds of friction eliminates the entire threat category.
Threat 3: Deepfake Executives
Video Calls Your Eyes Cannot Distinguish From Real
Deepfake technology places a real person’s face and voice onto fabricated video in real time. What required Hollywood resources five years ago now costs an attacker roughly $50 and a consumer laptop.
The attack: a staff member receives a video call from what appears to be the managing partner. Face right. Voice right. Mannerisms right. The “partner” explains a deal is closing and needs an urgent, confidential financial transaction processed immediately.
The financial damage is severe. But the more insidious threat is evidentiary: fabricated video evidence, false depositions, manipulated court submissions. Law firms are not just organizational targets — they are custodians of the legal record.
Defense requires a process, not just technology. Any unusual request received by video — especially one combining urgency and confidentiality — should trigger an out-of-band call on a pre-established number. The technology to fake a video call is accessible. The technology to simultaneously fake a phone call to a number you already have is not. AI-powered deepfake detection tools are also emerging as a necessary component of enterprise security stacks.
Threat 4: Automated Vulnerability Scanning
The Attacker Who Never Sleeps and Never Gets Tired
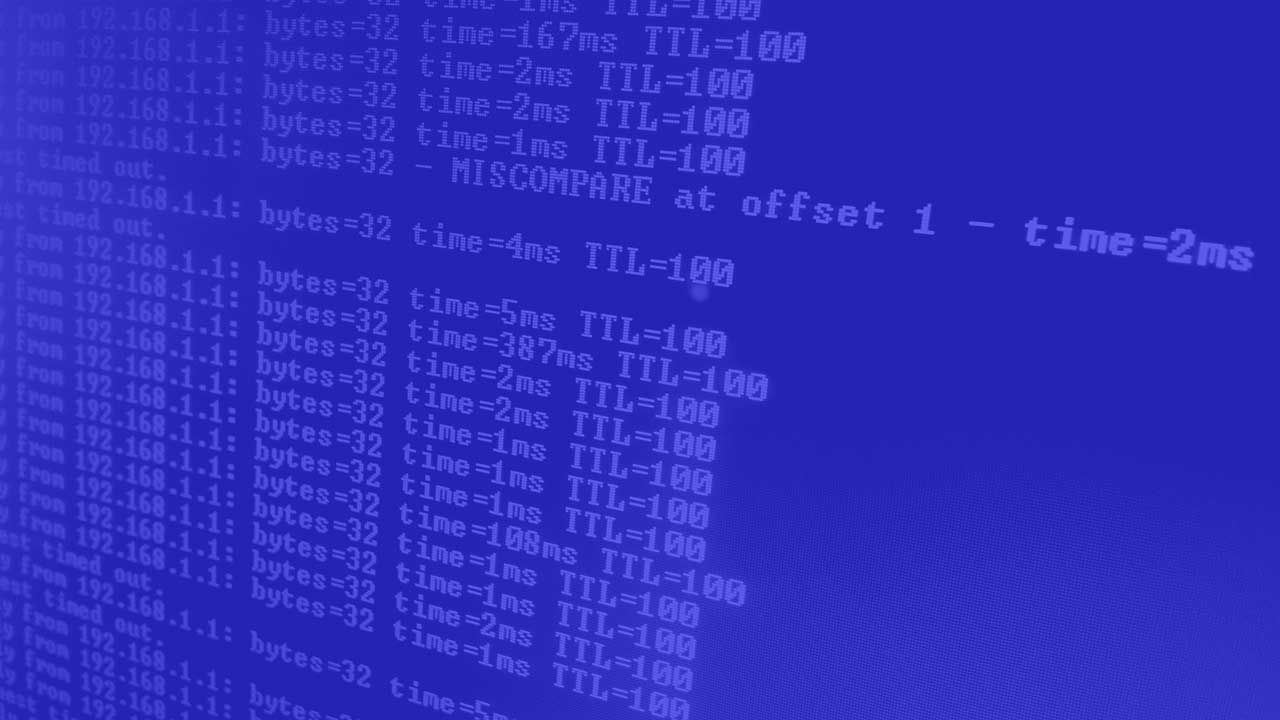
AI-powered scanning tools probe your entire digital footprint continuously, identifying unpatched software, misconfigured systems, exposed credentials, and open ports. When they find a weakness, they generate tailored exploits and either deploy them or sell access to specialists.
This automation has changed the economics of targeting law firms. Previously, attacking a small practice required significant human effort for modest return. Now, automated tools scan thousands of firms simultaneously and prioritize the weakest ones. Your firm doesn’t need to be targeted specifically, it just needs to appear vulnerable in a scan.
277 DAYS – Average time attackers are inside a network before discovery.
The timeline is the most alarming part. Attackers are frequently inside networks for months before anyone knows, reading emails, downloading files, and positioning ransomware for simultaneous deployment across every system. The “good enough” security posture: antivirus, a firewall, occasional patching, was designed for a world where attackers had to work for their access. It is not designed for this one.
The Question Your Firm Needs to Answer
Attackers are using AI offensively. The firms that survive 2026 are the ones using it defensively. Right now, only one side is bringing AI to this fight. The question is which side yours is on.