29
Sep
As well-seasoned technology professionals with over 60 years of combined technical experience, there’s not much our staff hasn’t seen and even less that’ll terrify us 

With full, unfettered access to an organization’s computer infrastructure, data, and back-end systems, we’re like the health inspector in the kitchen of your favorite restaurant careful to document what we see without causing panic in the dining room.
And, like a doctor beholden to the strictest patient confidentiality rules, we’re always careful to never divulge what we observe. Until now…
In the spirit of Halloween, we’ve compiled a few of the most terrifying encounters with systems that will make the wire on your non-wireless keyboard stand up in terror!
☠️ Proceed with caution! You’ve been warned!! ☠️
1) Door-to-door terror
An “unafraid” outside salesmen in 2014, I was always up for canvasing an office park–knocking on a few doors and seeing who might need help with their IT. While I was witness to many sketchy setups, the image that will forever stick in my head is the office manager convincing himself that their setup was “fine” as he literally struggled to talk over the intense buzz of assorted IT equipment stacked haphazardly in a closet of their 700 sq. ft. office located on the second floor of an old office building in Paramus, NJ.
The machines were “being kept cool” by a dust covered box-fan that hung precariously by a worn-out rope, tied-off to a small hook – halfway leaning out of a wall and obviously straining under the weight of the swaying fan. What kept that setup together, and their entire system from melting under the heat of that stuffy office I have no clue.
I was never able to close them on a new technology system. I truly believe my job isn’t to convince someone to change, only to help those that understand they need to. I wonder whatever happened to that company…
2) A Data Disaster
For an architect starting a business in 2008, technology mostly meant external hard-drives and an iMac Pro.
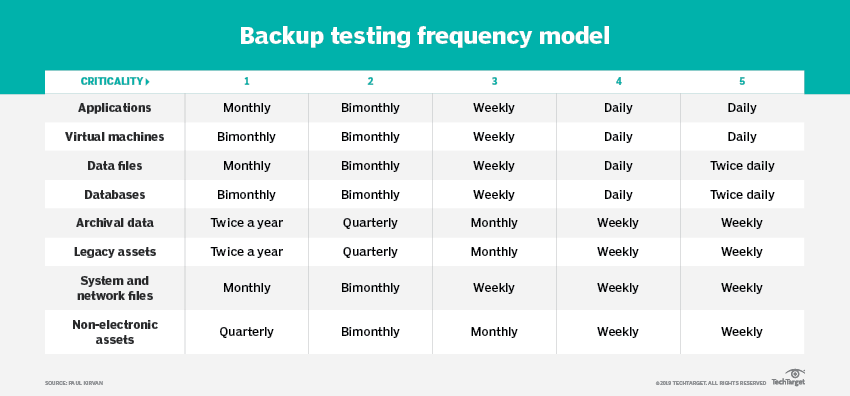
If you were fortunate enough to grow, IT solutions should grow at your pace but you could of course duck those upgrades and get away with expensive machines and cheap storage – the problem with that is that all machines (even the expensive one’s) stop working. And all data (even the cheep kind) needs to be backed up. When that lesson takes ten or 12 years to learn, the experience is terrifying
As the account manager, I was brought in post-sale to deal with a disaster of old machines and a hodgepodge of data sticks and external hard drives. The client, now a team of five full-timers, two interns and a part-time bookkeeper needed to get organized, and the project took years off my life! Sorting, sifting, looking, lifting – it was pure torture, but we got it done.
What I learned: watching a creative run a business can be horrifying, especially when the business is successful – despite the owners (what seems) like best attempts to keep them a decade behind in technology.
3) The Mystery of the Ethernet
“The computer in the back doesn’t have internet,” said the receptionist as I entered the office. Seemed simple enough; check the cables, unplug it, plug it back in – the usual steps for resolution stirred in my head. I found the sad and dirty little computer in a neglected corner of the service center.
Ethernet cord? Plugged in both on the computer and into an unlabeled jack haphazardly laying near the wall. The cable itself tested fine, but the jack was not providing internet. Ok, I try a different port, then another, and then yet another. I find a different set of possible ports and none could provide internet.
Where did these ethernet ports go? I tried using a tool to get an idea, but it wasn’t telling me anything. I ran my fingers along various filthy and tangled cables in a futile attempt to see where they might be going. Into the ceiling? Into the wall? It wasn’t at all clear.
I made a few calls and was directed to an unassuming closet. I opened the door to pure IT horror: power strips plugged into other power strips, a rats nest of wires (and evidence of actual rats), random pieces of equipment plugged into one another with no real explanation of why, mystery stains, warped shelves, trash – and most importantly – no clear answer to how anything was getting internet in that entire office.
It took an extra IT technician, an afternoon of finding/tracing/labeling, and lots of hand sanitizer to get to the bottom of it. Like an actual nightmare, it was hard to tell what was really happening and exactly what caused the issue to finally resolve itself, but without warning lights flashed green and, just like that, the “old computer in the back” had internet!
It’s 2022, if your technology is your brand, what does your IT strategy and infrastructure say about you?
You may not be as bad off as some of these folks, but is your setup fast? Is it secure? Is it easy for everyone to access? Is it highly available? Is it redundant? Why not?
Drop your name and email below to learn more, or tag my calendar to setup a
conversation.